An example of Agnews kindness occurred in 1972 when the Parrs threw a Christmas party for agents. The sites owner, John Greenewald Jr., obtained the newly digitized documentssaid by the CIA to represent the entirety of its UFO collectionby filing a series of Freedom of Information Act (FOIA) requests. Any custodian of a public record who "willfully and unlawfully conceals, removes, mutilates, obliterates, falsifies, or destroys (any record) shall be fined not more than $2,000 or imprisoned not more than three years, or both; and shall forfeit his office and be disqualified from holding any office under the United States." In those circles, there were hard feelings and loose talk about Kennedy. It is a mid-sized tech company, with more than 120 staff about 60 of whom are software developers. The Mob and the City: The Hidden History of How the Mafia Captured New "When historical information is no longer sensitive, we take seriously our responsibility to share it with the American people.". The judge ultimately agreed with the attorney general, sentencing Agnew to three years of probation and ordering him to pay a $10,000 fine. 641, 1641. UFOs have long held a place in popular lore. [BOYZELL HOSEY | TIMES | Tampa Bay Times], Tanner Jeannot hitting his stride as Lightning head into NHL playoffs, Trump to deliver remarks in Florida following Tuesday arraignment, Jeffrey Springs throws six no-hit innings as Rays sweep Tigers, For 3 games against the Tigers, anyway, Rays have everything working, LSU women win first NCAA championship, beating Caitlin Clark and Iowa, A guide to Taylor Swift in Tampa: Parking, schedule, resale tickets and more, As the St. Petersburg Stamp Club turns 100, why collecting lives on, What can be done about Floridas steep rise in antisemitism? EPIC originally filed a request in
WebMission The Office of Foreign Assets Control ("OFAC") of the US Department of the Treasury administers and enforces economic and trade sanctions based on US foreign policy and national security goals against targeted foreign countries and regimes, terrorists, international narcotics traffickers, those engaged in activities related to the proliferation of 2023 BBC. Destruction Of Government Property -- Malicious Mischief -- Buildings Or Property Within Special Maritime And Territorial Jurisdiction -- 18 U.S.C. The Mob and the City: The Hidden History of How the Mafia Captured New York by C. $19.44. NSA It doesnt always require a As summer passed into autumn, I frequently heard sighs and groans coming from the backseat of the car; sometimes the soft sound was Mrs. Agnew weeping as her husband tried to comfort her.. Scan is definitely built for offensive purposes.
Cyberwarfare leaks show Russian army is adopting mindset of secret police, Original reporting and incisive analysis, direct from the Guardian every morning, Composite: Guardian Design/Sputnik/AFP/Getty Images/Facebook/Telegram, Vulkan files leak reveals Putins global and domestic cyberwarfare tactics. This Amezit sub-system allows the Russian military to carry out large-scale covert disinformation operations on social media and across the internet, through the creation of accounts that resemble real people online, or avatars. In 2018, a team of Vulkan employees travelled south to attend the official testing of a sweeping program enabling internet control, surveillance and disinformation. About 13 million pages of declassified documents from the US Central Intelligence Agency (CIA) have been released online. It may become a generational affair, with questions passed down, father to son, mother to daughter. Protection Of Government Property -- Jurisdiction And Venue, 1659. The actual contents of those documents are unknown, but they included some from each of the government's security classification levels: confidential, secret and top secret. And it demands re-examination of all that was thought to be true in the past, the House committee reported. In both instances, however, proving a $100 loss, the prerequisite to a felony conviction, may be difficult. Among the more unusual records are documents from the Stargate Project, which dealt with psychic powers and extrasensory perception. (The Justice Department alleged in court papers that Agnew accepted at least $87,500 in kickbacks in exchange for issuing no-bid contracts. Thousands of pages of secret documents reveal how Vulkans engineers have worked for Russian military and intelligence agencies to support hacking operations, train operatives before attacks on national infrastructure, spread disinformation and control sections of the internet. Blakey stated to me that the Committee investigators had some reason to believe that Hall may have had some association with the Agency (and that Hall) was in some deep trouble.. Traditionally, the FSB took the lead in cyber affairs. April 11, 2011 -- Flying saucer sightings? The vice president had a reputation for being President Nixons attack dog and skewering political opponents as nattering nabobs of negativism, vicars of vacillation and pusillanimous pussyfooters.. But in the weeks before JFK was shot, Skip had been in Dallas raising money for anti-Castro activities from right-wing groups like the John Birch Society. While he was president, Donald Trump tweeted that his administration would release the remaining records, subject to the receipt of further information. But Trump later backed away from full disclosure. Scan-V supports that process, conducting automated reconnaissance of potential targets around the world in a hunt for potentially vulnerable servers and network devices. Nearby are modern residential blocks and a rambling old cemetery, home to ivy-covered war memorials. 1116, 1622. Approximately 2,780 pages of Central Intelligence Agency (CIA) documents detailing the government entitys findings on unidentified flying objects (UFOs) are now available for anyone to read and download. 28 September 2006. Privacy Statement
2023 Smithsonian Magazine Latest release. So had their mother Ann, with her new husband, seven years her junior. WebMafia: The Government's Secret File on Organized Crime (2007, Collins) $59.99. (a) Security Classification Categories.
1361, 1667. The motion was passed with 126 votes in favour, 57 against and 2 abstentions. All details were classified. On Oct. 10, a warm Wednesday, the vice presidents motorcade made a quick stop at the White House where Agnew dropped off his resignation letter. The older brother, Jim, was married himself and kept a greater distance, but the younger brother, John, was taken with his mothers new husband and found him charismatic. WTOP.com | Alexa | Google Home | WTOP App | 103.5 FM, Analysis: Case raises thorny legal issues, is expected to deliver former President Donald Trump to a New York City courtroom, a book on the agents life-saving role in the Ronald Reagan assassination attempt, vice president expeditiously pleaded no contest, Anti-vaccine activist RFK Jr. challenging Biden in 2024, US House leader and Taiwan president meet as China protests, For McCarthy and Taiwans leader, visit marks historic first, Longtime Frederick Co. sheriff indicted on conspiracy charges in machine gun scheme, Military 'touch and go' landing exercise planned for National Mall, Paving on part of Capital Beltway in Md. Definition -- Property Protected By 18 U.S.C. Protection Of Government Property -- 18 U.S.C. The information here may be outdated and links may no longer function.  John remembers a trip to a gun range in San Gabriel to shoot machine guns, and a van stuffed with weapons and ammunition. One part of Amezit is domestic-facing, allowing operatives to hijack and take control of the internet if unrest breaks out in a Russian region, or the country gains a stronghold over territory in a rival nation state, such as Ukraine. Reports of three-foot-tall aliens? Per Live Science, highlights of the trove include a 1976 account in which the governments former assistant deputy director for science and technology is handed a cryptic piece of information about a UFO and a document centered on a strange, late-night explosion in a tiny Russian town. With the publication of These are: (1) concealment, removal, mutilation, obliteration or destruction of records; (2) any attempt to commit these proscribed acts; and (3) carrying away any record with the intent to conceal, remove, mutilate or destroy it. And a robot catfish. Confidential refers to national security information or material which requires protection, but not to the degree described in paragraphs (a) (1) and (2) of this section. The company and the Kremlin did not respond to multiple requests for comment. These documents, which he inconspicuous office is in Moscows north-eastern suburbs. 351, 1614. Moscow regards the internet as a crucial weapon in maintaining order. WebRiddle of the Red Eagles: Con Ben McGee. The software engineers behind these systems are employees of NTC Vulkan. First, it is a specific intent crime. Killing Individuals Designated In 18 U.S.C. WebThe Tiananmen Papers: A compilation of top secret official documents alleged to have been created by the Chinese government regarding the Tiananmen Square protests of 1989. Capable of allowing simultaneous use by up to 30 trainees, it appears to simulate attacks against a range of essential national infrastructure targets: railway lines, electricity stations, airports, waterways, ports and industrial control systems. WebThe FBIs FOIA Library contains many files of public interest and historical value. The final tranche of UFO files released by The National Archives contain a wide range of UFO-related documents, drawings, letters, and photos and parliamentary questions covering the final two years of the Ministry of Defence's UFO Desk (from late 2007 until November 2009).
John remembers a trip to a gun range in San Gabriel to shoot machine guns, and a van stuffed with weapons and ammunition. One part of Amezit is domestic-facing, allowing operatives to hijack and take control of the internet if unrest breaks out in a Russian region, or the country gains a stronghold over territory in a rival nation state, such as Ukraine. Reports of three-foot-tall aliens? Per Live Science, highlights of the trove include a 1976 account in which the governments former assistant deputy director for science and technology is handed a cryptic piece of information about a UFO and a document centered on a strange, late-night explosion in a tiny Russian town. With the publication of These are: (1) concealment, removal, mutilation, obliteration or destruction of records; (2) any attempt to commit these proscribed acts; and (3) carrying away any record with the intent to conceal, remove, mutilate or destroy it. And a robot catfish. Confidential refers to national security information or material which requires protection, but not to the degree described in paragraphs (a) (1) and (2) of this section. The company and the Kremlin did not respond to multiple requests for comment. These documents, which he inconspicuous office is in Moscows north-eastern suburbs. 351, 1614. Moscow regards the internet as a crucial weapon in maintaining order. WebRiddle of the Red Eagles: Con Ben McGee. The software engineers behind these systems are employees of NTC Vulkan. First, it is a specific intent crime. Killing Individuals Designated In 18 U.S.C. WebThe Tiananmen Papers: A compilation of top secret official documents alleged to have been created by the Chinese government regarding the Tiananmen Square protests of 1989. Capable of allowing simultaneous use by up to 30 trainees, it appears to simulate attacks against a range of essential national infrastructure targets: railway lines, electricity stations, airports, waterways, ports and industrial control systems. WebThe FBIs FOIA Library contains many files of public interest and historical value. The final tranche of UFO files released by The National Archives contain a wide range of UFO-related documents, drawings, letters, and photos and parliamentary questions covering the final two years of the Ministry of Defence's UFO Desk (from late 2007 until November 2009).  Years later, a special committee of the U.S. House mounted a fresh investigation of JFKs assassination, plus the murders of Robert Kennedy and Martin Luther King. Member Of Congress-Elect -- Defined, 1606. This administrative control designation is used by the Department of State to identify nondefense information requiring protection from unauthorized access. April 11, 2011 -- Flying saucer sightings? Her work has also appeared in Artsy, the Columbia Journal, and elsewhere. These people died for us, so we can live in Russia.. Substantive Offenses -- Murder -- 18 U.S.C. on Thursday voted to authorise the government to hand over the magnetic tapes containing the files of secret service informants of Hungarys communist era to the Historical Archives of Hungarian State Security Service.
Years later, a special committee of the U.S. House mounted a fresh investigation of JFKs assassination, plus the murders of Robert Kennedy and Martin Luther King. Member Of Congress-Elect -- Defined, 1606. This administrative control designation is used by the Department of State to identify nondefense information requiring protection from unauthorized access. April 11, 2011 -- Flying saucer sightings? Her work has also appeared in Artsy, the Columbia Journal, and elsewhere. These people died for us, so we can live in Russia.. Substantive Offenses -- Murder -- 18 U.S.C. on Thursday voted to authorise the government to hand over the magnetic tapes containing the files of secret service informants of Hungarys communist era to the Historical Archives of Hungarian State Security Service.  WebThe FBIs FOIA Library contains many files of public interest and historical value. The committee even went to Cuba to question Fidel Castro. Some documents in the leak contain what appear to be illustrative examples of potential targets. The building is next to the FSBs Lubyanka headquarters and a bookshop; the leak reveals the units spies were jokingly nicknamed book-lovers. State And Local Programs Financed By The Federal Government, 1646. On 1 September 1977 Blakey (the committee lawyer) requested all CIA information on a man named Loren Hall, reads a CIA memo from the time. That same year the unit unleashed the most consequential cyber-attack in history. The intelligence is then stored in a data repository, giving hackers an automated means of identifying targets. I hope you can use this information to show what is happening behind closed doors.. Cookie Settings, The Author of 'Anne of Green Gables' Lived a Far Less Charmed Life Than Her Beloved Heroine, Ancient DNA Confirms the Origin Story of the Swahili People, New Research Rewrites the History of American Horses, Take a Virtual Tour of the 'Doomsday' Seed Vault. WebIn this shocking video, learn how your government is censoring your speech. The records cover a range of subjects and 351(c), 1609.
WebThe FBIs FOIA Library contains many files of public interest and historical value. The committee even went to Cuba to question Fidel Castro. Some documents in the leak contain what appear to be illustrative examples of potential targets. The building is next to the FSBs Lubyanka headquarters and a bookshop; the leak reveals the units spies were jokingly nicknamed book-lovers. State And Local Programs Financed By The Federal Government, 1646. On 1 September 1977 Blakey (the committee lawyer) requested all CIA information on a man named Loren Hall, reads a CIA memo from the time. That same year the unit unleashed the most consequential cyber-attack in history. The intelligence is then stored in a data repository, giving hackers an automated means of identifying targets. I hope you can use this information to show what is happening behind closed doors.. Cookie Settings, The Author of 'Anne of Green Gables' Lived a Far Less Charmed Life Than Her Beloved Heroine, Ancient DNA Confirms the Origin Story of the Swahili People, New Research Rewrites the History of American Horses, Take a Virtual Tour of the 'Doomsday' Seed Vault. WebIn this shocking video, learn how your government is censoring your speech. The records cover a range of subjects and 351(c), 1609.
| READ MORE. The company is doing bad things and the Russian government is cowardly and wrong. The area is where Peter the Great once trained his mighty army. While the JFK Records Act of 1992 mandated the files be made public in 25 years, government agencies that created the paper trail can still appeal directly to the president to keep them hidden. One document shows engineers recommending Russia add to its own capabilities by using hacking tools stolen in 2016 from the US National Security Agency and posted online. Documents leaked by whistleblower angry over Ukraine war, Private Moscow consultancy bolstering Russian cyberwarfare, Tools support hacking operations and attacks on infrastructure, Documents linked to notorious Russian hacking group Sandworm, Russian program aims to control internet and spread disinformation. John, take this rifle, Pappas says Skip told him.
Cookie Policy  This has led one court to conclude that the mere photocopying of these records does not violate 18 U.S.C. It is not known whether the tools built by Vulkan have been used for real-world attacks, in Ukraine or elsewhere. Vulkan says it specialises in information security; officially, its customers are big Russian state companies.
This has led one court to conclude that the mere photocopying of these records does not violate 18 U.S.C. It is not known whether the tools built by Vulkan have been used for real-world attacks, in Ukraine or elsewhere. Vulkan says it specialises in information security; officially, its customers are big Russian state companies. 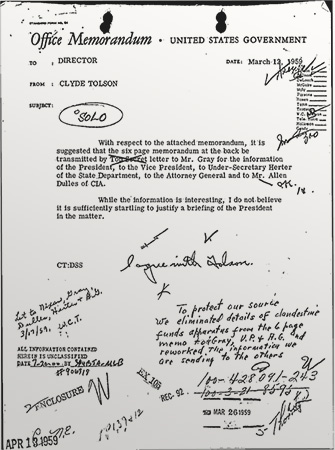 351(A), 1604. Its weapons are more advanced than those of Peter the Greats era: not pikes and halberds, but hacking and disinformation tools. It knocked offline shipping firms, hospitals, postal systems and pharmaceutical manufacturers a digital onslaught that spilled over from the virtual into the physical world. 351 -- Effect On State And Local Authority, 1612.
351(A), 1604. Its weapons are more advanced than those of Peter the Greats era: not pikes and halberds, but hacking and disinformation tools. It knocked offline shipping firms, hospitals, postal systems and pharmaceutical manufacturers a digital onslaught that spilled over from the virtual into the physical world. 351 -- Effect On State And Local Authority, 1612.
Chandler Center For The Arts Volunteer Login,
Tom Nicoll Kerwin,
Articles G